Use Gingr Pet Business Software for Pawesome Results
Gingr makes running a pet-care business a walk in the dog park. Create exceptional employee, customer, and pet experiences with solutions designed specifically for your industry. Explore the unique benefits and innovative features Gingr’s pet business software has to offer.

Benefits of Using Pet Business Software
When your pet-care business thrives, tails wag harder! Gingr gives you the tools to manage your day-to-day while growing your bottom line.
Maximize Revenue
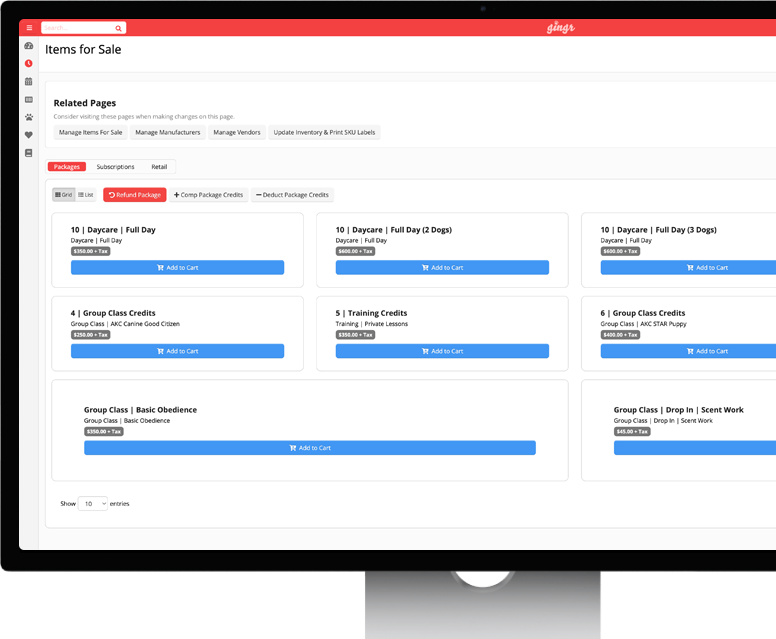
Boost your earnings with smart tools that increase upsells, reduce no-shows, and automate peak pricing. Gingr’s online booking and integrated payments features make sure your business never misses a beat—or a buck.
Optimize Operations
Simplify your processes, save time, and boost efficiency. Whether it’s managing appointments and lodging calendars, handling payments, or enabling pet parents to PreCheck, Gingr helps you cut the busywork and focus on what really matters: pets.
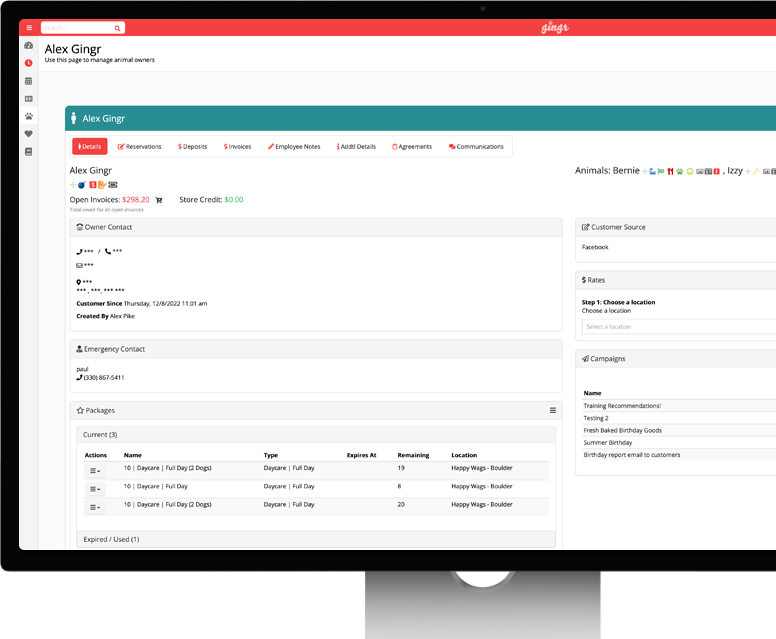
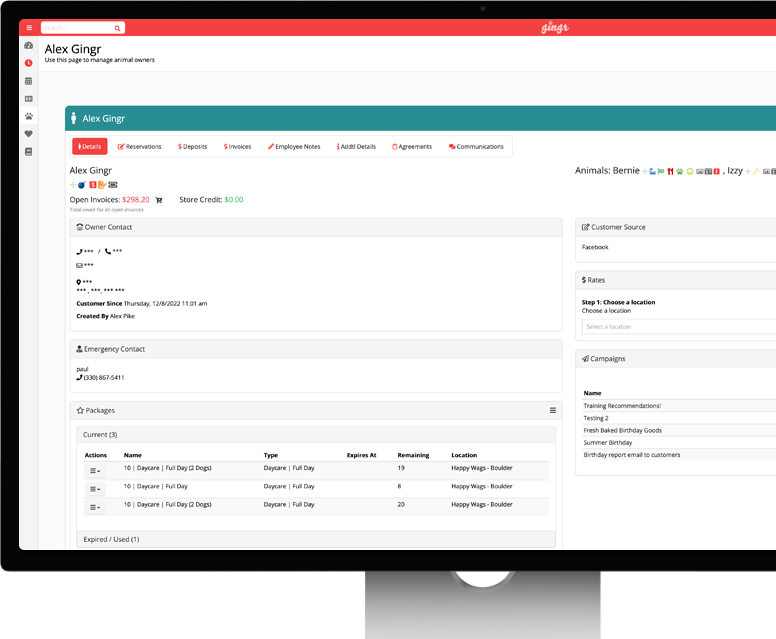
Build Customers for Life
Turn one-time visits into lifelong relationships. Gingr’s customer engagement features—from loyalty rewards to automated appointment reminders and report cards—keep pet parents informed. The result? Happy pets, loyal customers, and a growing business!
Pet Business Software Features That Help You Grow
Designed to take your pet-care business to the next level, Gingr’s features ensure you have everything you need to succeed in one powerful platform.
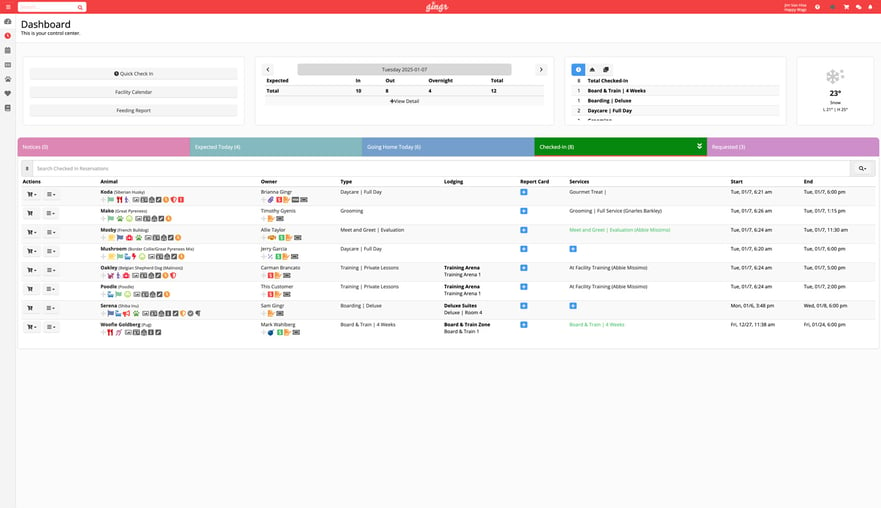
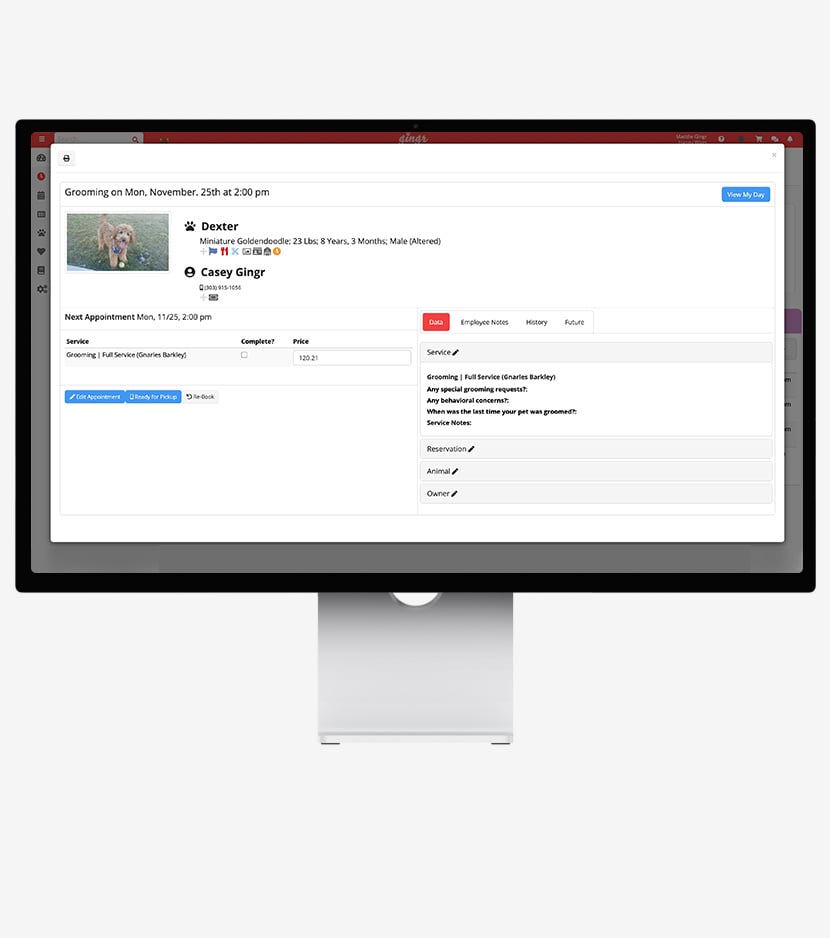
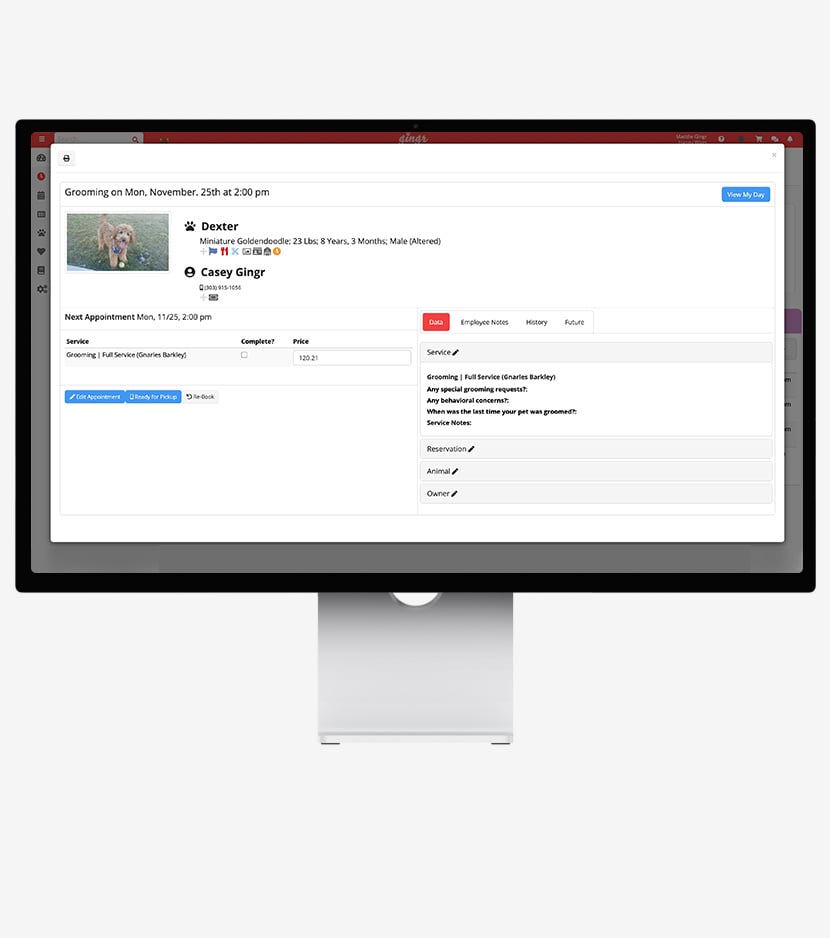
Pet Scheduling Software
Effortlessly manage pet daycare, boarding, grooming, and more with intuitive drag-and-drop calendars. Each pet comes with their own appointment card, complete with all the details you need.
- Book appointments
- Pay invoices
- Receive reminders and notifications
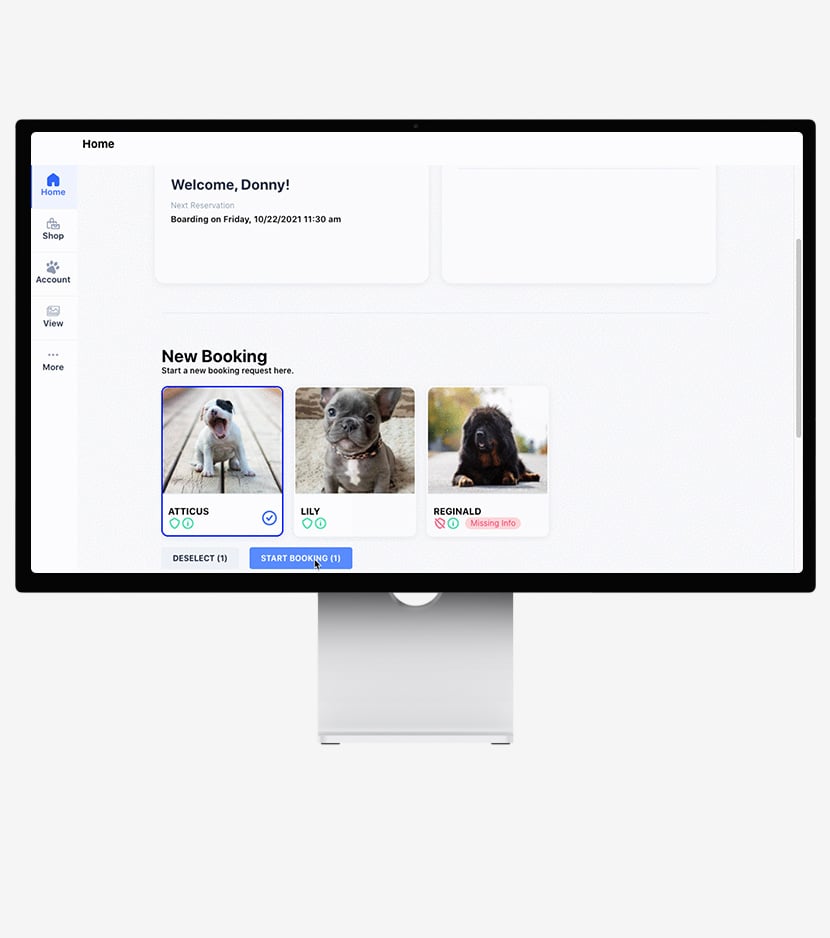
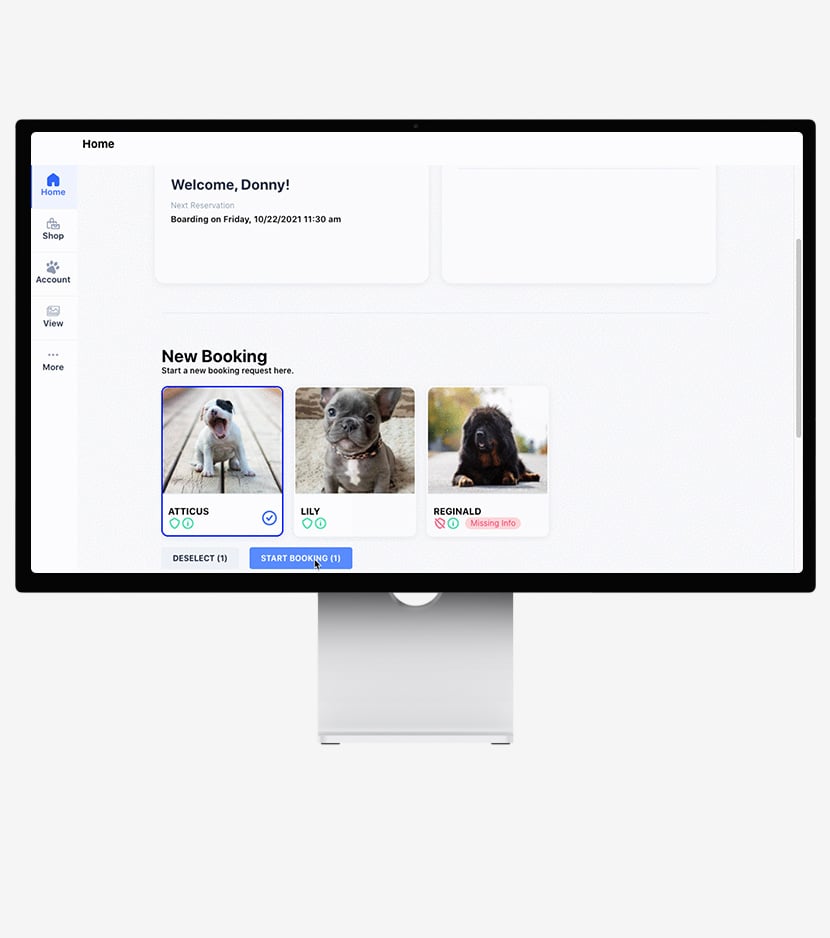
Pet Parent Mobile App
Who doesn’t rely on their phone to manage their life these days? Give your customers the power to book and track appointments with ease.
- Book appointments
- Pay invoices
- Receive reminders and notifications
.png)
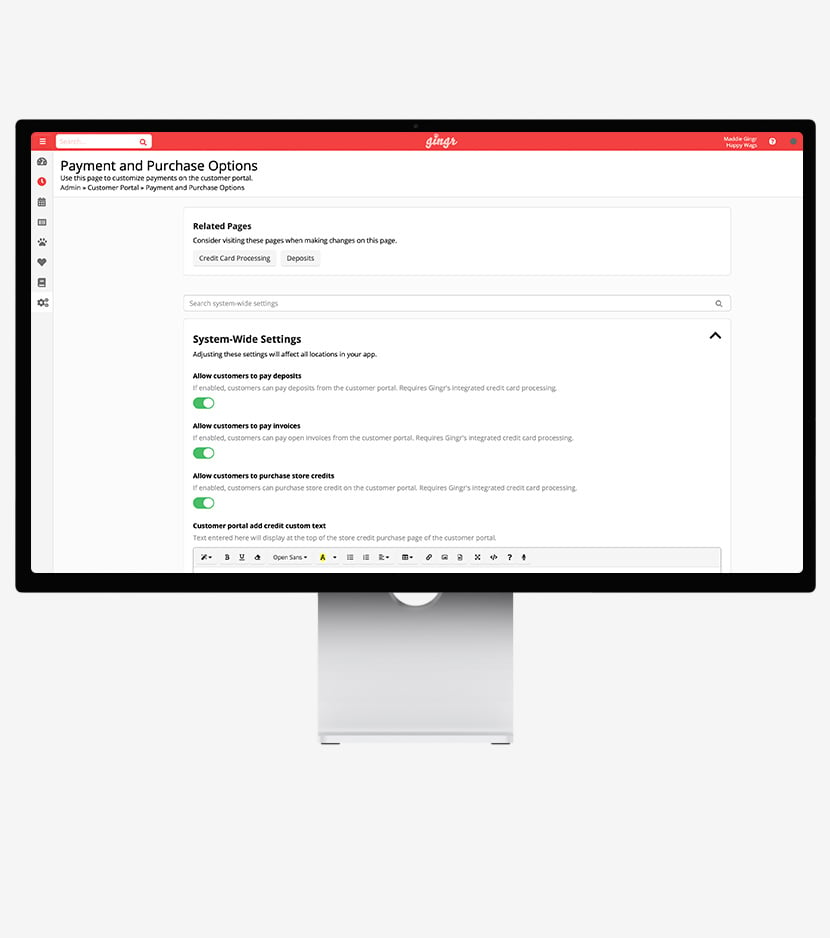
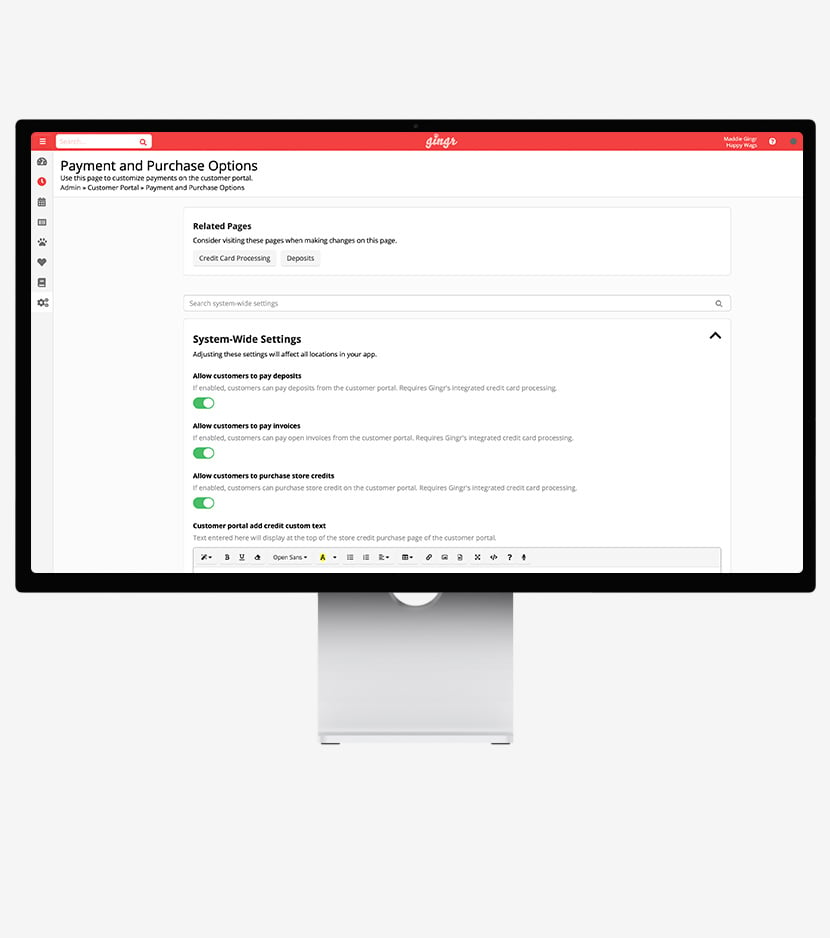
Integrated Payment Processing
Secure, seamless payments keep things moving. Automated pricing rules and invoicing ensure you get paid the right amount for every reservation. No time-consuming math equations required!
- Secure mobile payment collection
- Cash drawer and receipt printer integration
- Faster transactions
Gingr PreCheck
Reduce waiting-room chaos with faster check-ins. Free up your staff’s time by having pet parents complete a detailed check-in form in advance.
- Online, self-serve portal
- Curbside check-in
- Automatic “I’m here!” notifications
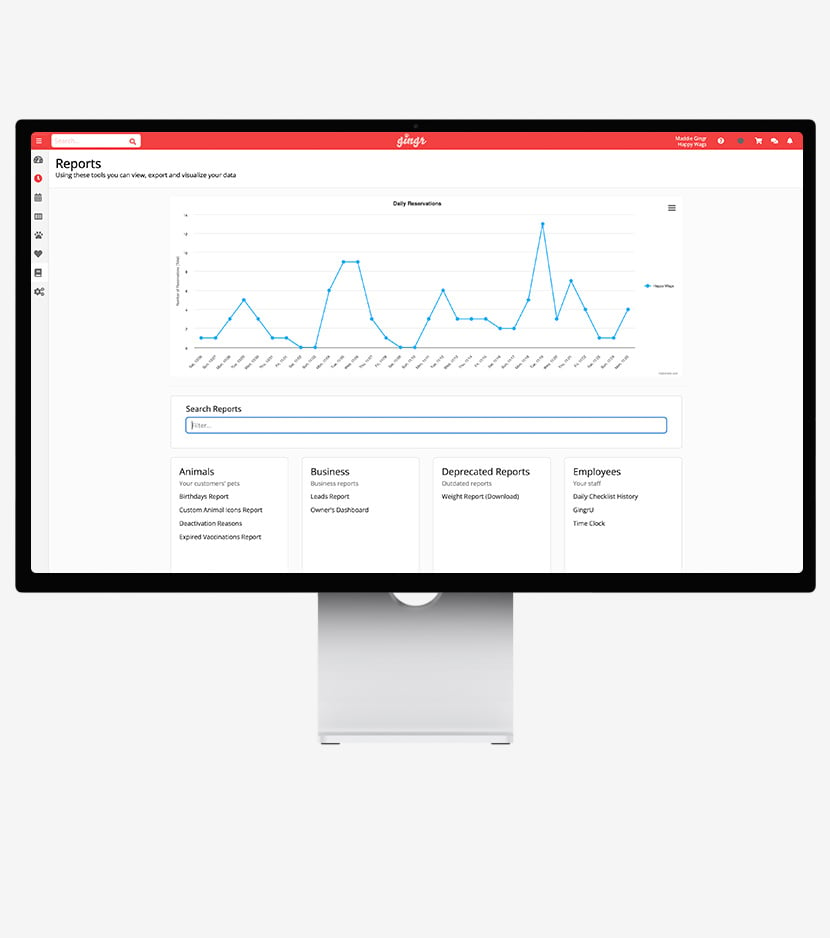
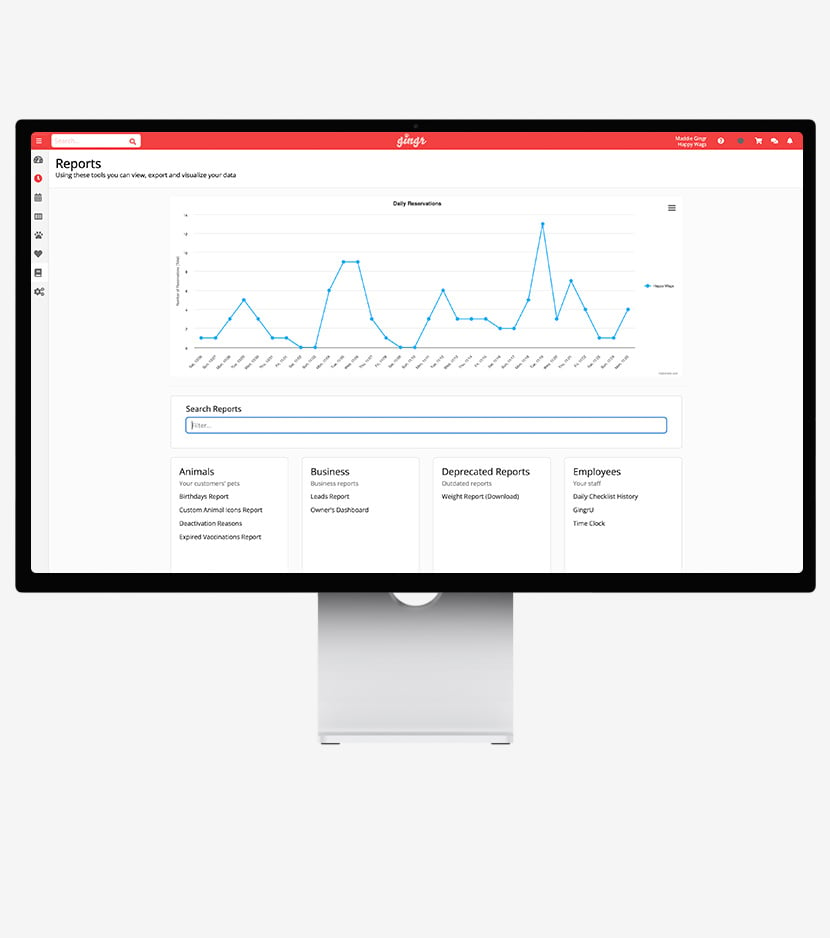
Business Analytics
Leverage your pet business software to create detailed reports that help you identify insights, make informed decisions, and oversee your business like the pros.
- Period-by-period comparative reports
- Multi-location data in one place
- Booking source insights
.png)
Pet Business Software FAQs
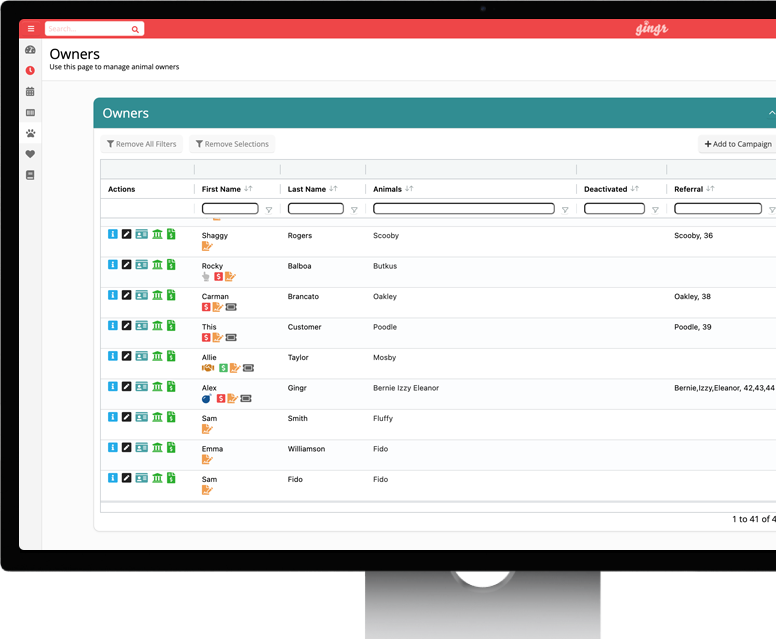
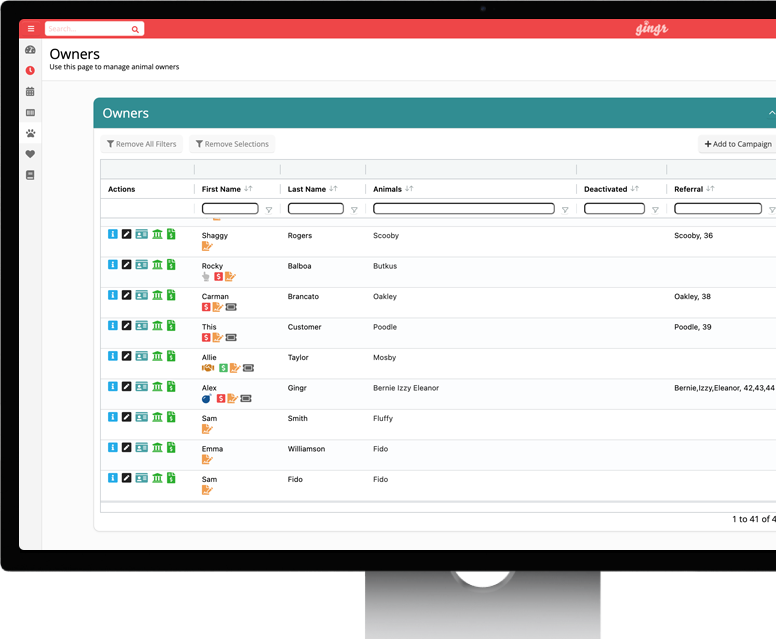
No, Gingr is a true all-in-one pet business software solution that meets all unique pet industry needs. For example, Gingr makes it easy to manage lodging and kennel capacity, grooming appointments, daycare groups, and multi-session training classes with a single account.
This way, you won’t need to pay for multiple subscriptions, transfer data manually across solutions, or worry about mistakes like double booking. Your records will always be up-to-date and accessible to staff. This means if a boarding dog needs an exit bath, your grooming team will see it instantly.
Switching software can feel daunting, and it can be an expensive, lengthy process. To help you smoothly migrate to Gingr, we have a dedicated onboarding team to guide you through the process. We offer data migration assistance to help transfer your existing records—including client lists, pet profiles, and future reservations—from your legacy system and into Gingr.
Our goal is to minimize downtime and preserve your data, allowing you to keep your business running smoothly while upgrading your operations.
Yes! Gingr is fully customizable for all pet types, including dogs, cats, and exotic pets. You can configure Gingr to suit a cat-only boarding cattery, an exotic pet hotel, a mixed-animal facility, or any other pet business you might run. Our core features, like scheduling and payments, apply to any animal or pet care business.
Explore this customer story to see how Club Cat used Gingr to level up its cat boarding business.
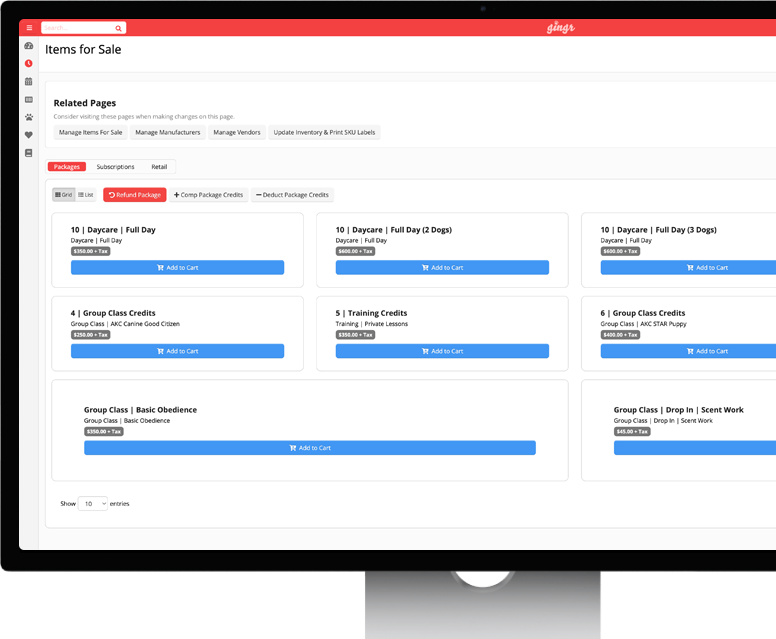
Yes, Gingr offers retail management features to help you track inventory levels for food, toys, accessories, grooming tools, and other supplies. Ensure your inventory aligns with customer demand by setting reorder points to prevent stockouts. When an item is sold through our integrated Point of Sale (POS), the inventory count updates automatically to keep your records organized and accurate.
Not at all! Gingr is designed to scale with you as your business evolves, and we are prepared to help you grow from a single facility to a multi-location enterprise business. Adding a new location is a big step for your business, but making the change in Gingr is simple.
Additionally, our enterprise solution allows you to manage reporting, staff, and customer profiles across all locations from a single login. This way, you never have to switch between different accounts or platforms as you expand. To learn more, browse our enterprise solution offerings.


